Cybercriminals are luring customers into downloading malware via faux AI turbines. After a person uploads their very own picture as a immediate, the web site offers a downloadable file containing an infostealer.
“This file installs malware — comparable to Noodlophile or Noodlophile bundled with XWorm — onto their programs, enabling attackers to steal information, harvest credentials, and probably acquire distant entry to contaminated units,” wrote Shmuel Uzan, a safety researcher for Morphisec, in a report.
Faux AI instruments are marketed on Fb
The brand new type of social engineering seems to begin on Fb, as attackers promote hyperlinks to “AI-themed platforms” in teams the place members are looking for free AI instruments. These teams have hundreds of members, and posts in them can attain as much as 62,000 views, in response to Uzan.
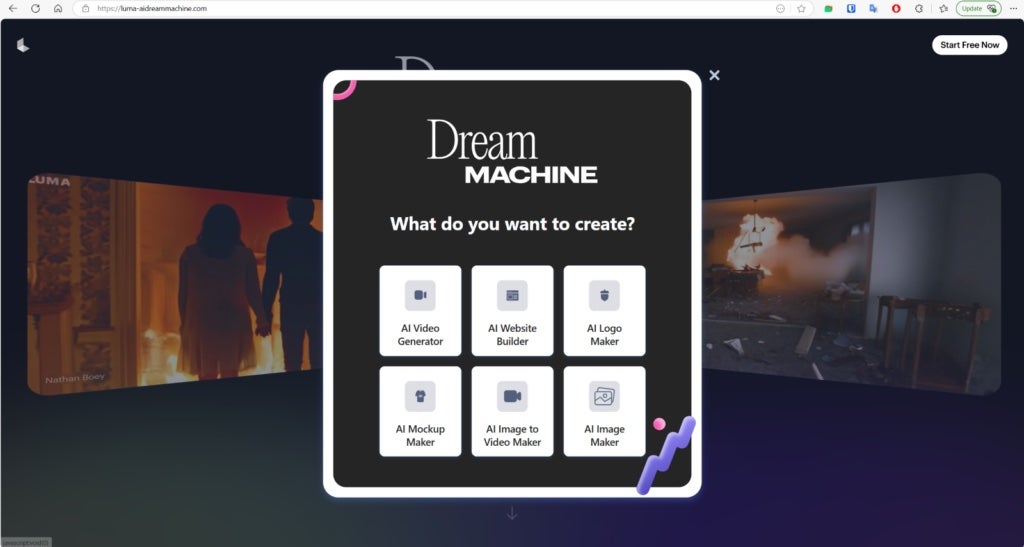
The bogus web sites the place victims search entry to the promised AI companies mimic professional software program, misusing names and logos comparable to Luma Dream Machine. One even contains the CapCut brand, a preferred video enhancing app owned by TikTok mum or dad firm ByteDance.
The web sites encourage guests to add their very own photographs or movies, claiming that AI will likely be used to edit the recordsdata or generate new content material utilizing them as a immediate. As soon as uploaded, the platform “processes” the reference file after which presents a Obtain Now button.
SEE: TechRepublic Premium’s Malware Fast Glossary
When victims attempt to obtain their AI-generated content material, they get contaminated
When the sufferer clicks the button, they obtain a ZIP file named VideoDreamAI.zip, which comprises a sequence of elements, together with a .NET loader, C++-based executables, and batch scripts. One executable, Video Dream MachineAI.mp4.exe, launches the second, CapCut.exe, which subsequently runs the .NET loader.
The loader downloads a Python payload known as srchost.exe from a distant server, which, when executed, deploys an infostealer that harvests the sufferer’s browser credentials, cookies, crypto wallets, tokens, and different information. This has been dubbed the Noodlophile Infostealer, and might ship the stolen particulars to the attackers via a Telegram bot. In some circumstances, a distant entry trojan like XWorm can also be loaded.
Who’s being focused, and what makes this marketing campaign distinctive
Along with photographs and movies, the fraudulent platforms uncovered by Uzan provide AI-generated web sites and mockups, suggesting that the attacker’s targets are companies. Nevertheless, their use of Fb teams for promotion signifies they aren’t pursuing giant company shoppers, however relatively small or medium-sized companies searching for free instruments to chop advertising and marketing prices.
“What makes this marketing campaign distinctive is its exploitation of AI as a social engineering lure — turning an rising professional pattern into an an infection vector,” Uzan wrote. “Not like older malware campaigns disguised as pirated software program or recreation cheats, this operation targets a more moderen, extra trusting viewers: creators and small companies exploring AI for productiveness.”
Noodlophile is believed to originate in Vietnam
Trying to find the time period “Noodlophile” on cybercrime boards revealed that it was being marketed as a part of a malware-as-a-service providing, Uzan discovered. He additionally found the malware’s developer on Fb leaving feedback on posts that promoted an account takeover approach related to the Noodlophile infostealer.
As a result of language and different social media indicators, Uzan believes the developer is Vietnamese. The related GitHub profile, which has had the identify Noodlophile eliminated, says that they’re a “passionate Malware Developer” who sells cyber safety instruments.